security bit of tag rfid be locked by unauthorised party RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. View and Download LG V20 user manual online. V20 telephone pdf manual download. Also for: H910, Lg-us996 v20. . Drag to activate it. • Touch your device with other device that supports .
0 · security attacks on rfid
1 · rfid spoofing
2 · rfid security update
3 · protecting from rfid attack
4 · how to protect sensitive rfid
5 · how to protect rfid data
6 · how to prevent rfid
7 · advanced rfid protection
Contributor II. Hello guys, I am trying to read NDEF message from ISO 14443 .
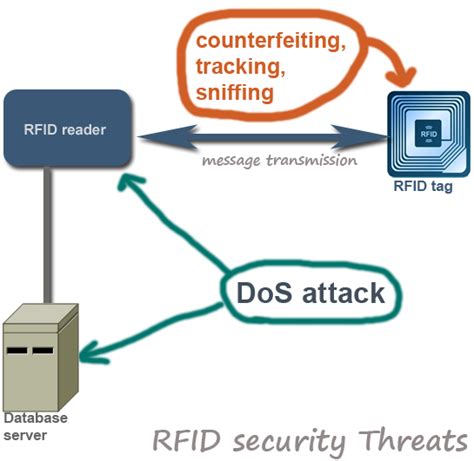
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities.
Eavesdropping, like it sounds, occurs when an unauthorized RFID reader listens to conversations between a tag and reader then obtains important data. It is still necessary for the hacker to know the specific protocols and tag and reader information for this technique to work. RFID tags, which are small, passive devices that contain a unique identifier and other data, can be susceptible to unauthorised access. Hackers can employ specialised equipment to read the information stored on an RFID tag, potentially compromising sensitive personal data such as credit card numbers, passport details, or even medical records.
Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID . Cloning and forgery are significant security risks associated with RFID technology, where attackers attempt to replicate or manipulate RFID tags for unauthorized access or malicious purposes.
contactless credit card tap to pay fraud
The best solution for this scenario is for employees to leave their card secured off their person (e.g. in their vehicle), away from the eyes and reach of potential attackers. If an employee does not have the ability to leave their badge in a secure location, an RFID blocking sleeve should be used.
Preventing Unauthorized Access: Implementing access controls and encryption protocols helps restrict unauthorized access to RFID data, ensuring that only authorized readers can retrieve information from RFID tags. A third practice is to lock your RFID tags to prevent unauthorized changes or erasure of the data. Locking is a feature that allows you to set different levels of access and protection for. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. Eavesdropping, like it sounds, occurs when an unauthorized RFID reader listens to conversations between a tag and reader then obtains important data. It is still necessary for the hacker to know the specific protocols and tag and reader information for this technique to work. RFID tags, which are small, passive devices that contain a unique identifier and other data, can be susceptible to unauthorised access. Hackers can employ specialised equipment to read the information stored on an RFID tag, potentially compromising sensitive personal data such as credit card numbers, passport details, or even medical records.
Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID . Cloning and forgery are significant security risks associated with RFID technology, where attackers attempt to replicate or manipulate RFID tags for unauthorized access or malicious purposes. The best solution for this scenario is for employees to leave their card secured off their person (e.g. in their vehicle), away from the eyes and reach of potential attackers. If an employee does not have the ability to leave their badge in a secure location, an RFID blocking sleeve should be used.
Preventing Unauthorized Access: Implementing access controls and encryption protocols helps restrict unauthorized access to RFID data, ensuring that only authorized readers can retrieve information from RFID tags.
security attacks on rfid
contactless cash card singapore
rfid spoofing
rfid security update
RFID Reader / Writer software. Hello guys, I'm currently working on a chapter for my school .
security bit of tag rfid be locked by unauthorised party|rfid spoofing