microsoft pki smart card Simplify and automate cloud certificate management using Microsoft Cloud PKI, included in the . BCARDTM Reader App on your NFC Smartphone/Tablet User supplies NFC Enabled device. .Remember that you still have to scan the watch with the phone to activate it and the phone still has to run the Libre app to pull the data from the sensor, even though it’s communicating via Bluetooth instead of repeated NFC scans. Now .
0 · smart card two factor authentication
1 · smart card computer access
2 · smart card authentication step by
3 · pki smarttoken
4 · pki smart card authentication
5 · fips 140 2 smart card
6 · authentication smart card
7 · adfs smart card authentication
Discover ID TECH’s complete payment solutions for today’s ever-changing payment .Just dip or tap to pay. Be ready for every sale with Square Reader for contactless and chip. More customers than ever are paying with contactless (NFC) cards, and over 95% of cards processed through Square are EMV chip cards. Every dip or tap payment is the same simple rate: 2.6% + .
The Smart Card Technical Reference describes the Windows smart card infrastructure for physical smart cards and how smart card-related components work in Windows. This document also contains information about tools that information technology (IT) developers and administrators can . See more Microsoft Entra users can authenticate using X.509 certificates on their smart .Simplify and automate cloud certificate management using Microsoft Cloud PKI, included in the .
This document explains how the Windows smart card infrastructure works. To understand this information, you should have basic knowledge of public key infrastructure (PKI) and smart card concepts. This document is intended for: Enterprise IT developers, managers, and staff who are planning to deploy or are using smart cards in their organization.
Microsoft Entra users can authenticate using X.509 certificates on their smart cards directly against Microsoft Entra ID at Windows sign-in. There's no special configuration needed on the Windows client to accept the smart card authentication.Simplify and automate cloud certificate management using Microsoft Cloud PKI, included in the Microsoft Intune Suite. You can enable a smart card logon process with Microsoft Windows 2000 and a non-Microsoft certification authority (CA) by following the guidelines in this article. Limited support for this configuration is described later in this article.
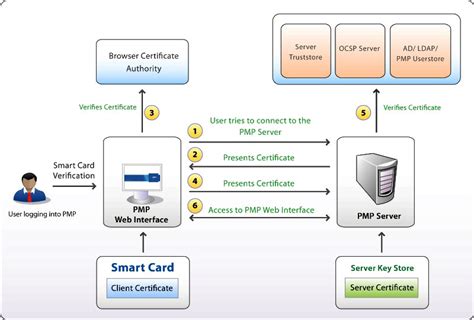
In this post, we will walk through step-by-step how you can set up and configure new or existing Microsoft PKI to support PIV smart card authentication including setting up an OCSP responder, proper configuration of Active Directory, domain controllers, certificate templates, group policy, and WorkSpaces.The CSPs are responsible for creating, storing and accessing cryptographic keys – the underpinnings of any certificate and PKI. These keys can be symmetric or asymmetric, RSA, Elliptical Key or a host of others such as DES, 3DES, and so forth.Certificate-Based Authentication (CBA) enables agencies to authenticate with X.509 certificates directly through Microsoft’s Entra ID, providing phishing-resistant authentication using x.509 certificates issued from their trusted Public Key Infrastructure (PKI). CVE-2022-34691, CVE-2022-26931 and CVE-2022-26923 address an elevation of privilege vulnerability that can occur when the Kerberos Key Distribution Center (KDC) is servicing a certificate-based authentication request.
To ensure that your organization can take full advantage of your Active Directory Certificate Services (AD CS) installation, you must plan the PKI deployment appropriately. You should determine how many CAs you need and in what configuration before you install any CA.
smart card two factor authentication

After the virtual smartcard creation it can be treated just like a traditional smart card by using the “Microsoft Base Smart Card Crypto Provider” or “Microsoft Smart Card Key Storage Provider”. Smart Card Logon Certificate Template . In this section we will create the certificate template to be used for smartcard logon. This document explains how the Windows smart card infrastructure works. To understand this information, you should have basic knowledge of public key infrastructure (PKI) and smart card concepts. This document is intended for: Enterprise IT developers, managers, and staff who are planning to deploy or are using smart cards in their organization.
smart card number tamilnadu
Microsoft Entra users can authenticate using X.509 certificates on their smart cards directly against Microsoft Entra ID at Windows sign-in. There's no special configuration needed on the Windows client to accept the smart card authentication.Simplify and automate cloud certificate management using Microsoft Cloud PKI, included in the Microsoft Intune Suite. You can enable a smart card logon process with Microsoft Windows 2000 and a non-Microsoft certification authority (CA) by following the guidelines in this article. Limited support for this configuration is described later in this article.
In this post, we will walk through step-by-step how you can set up and configure new or existing Microsoft PKI to support PIV smart card authentication including setting up an OCSP responder, proper configuration of Active Directory, domain controllers, certificate templates, group policy, and WorkSpaces.The CSPs are responsible for creating, storing and accessing cryptographic keys – the underpinnings of any certificate and PKI. These keys can be symmetric or asymmetric, RSA, Elliptical Key or a host of others such as DES, 3DES, and so forth.Certificate-Based Authentication (CBA) enables agencies to authenticate with X.509 certificates directly through Microsoft’s Entra ID, providing phishing-resistant authentication using x.509 certificates issued from their trusted Public Key Infrastructure (PKI).
smart card computer access
CVE-2022-34691, CVE-2022-26931 and CVE-2022-26923 address an elevation of privilege vulnerability that can occur when the Kerberos Key Distribution Center (KDC) is servicing a certificate-based authentication request. To ensure that your organization can take full advantage of your Active Directory Certificate Services (AD CS) installation, you must plan the PKI deployment appropriately. You should determine how many CAs you need and in what configuration before you install any CA.

smart card authentication step by

smart card payment method
smart card operating system application
These iPhones will read NFC tags without opening an App or .
microsoft pki smart card|smart card authentication step by