can rfid tags be hacked Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
Filter store by In-store appointments Mobile devices for business + consumer .
0 · rfid scam
1 · problems with rfid technology
2 · problems with rfid
3 · is rfid safe to hack
4 · is rfid dangerous
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
SwipeYours fills this space. SwipeYours is a small, self contained app from which your card data never leaves the phone except to make NFC payments. It uses the Visa-MSD .
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach .Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack .
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, . Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
There are several ways in which RFID hacking can occur: Eavesdropping: Attackers intercept and decode the radio signals exchanged between the tags and readers, gaining unauthorized .RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .
structure of smart card
Keeping key cards in a reader proof wallet or case will help prevent skimming, where an attacker gets close enough with an NFC or RFID reader. Most importantly, physical .
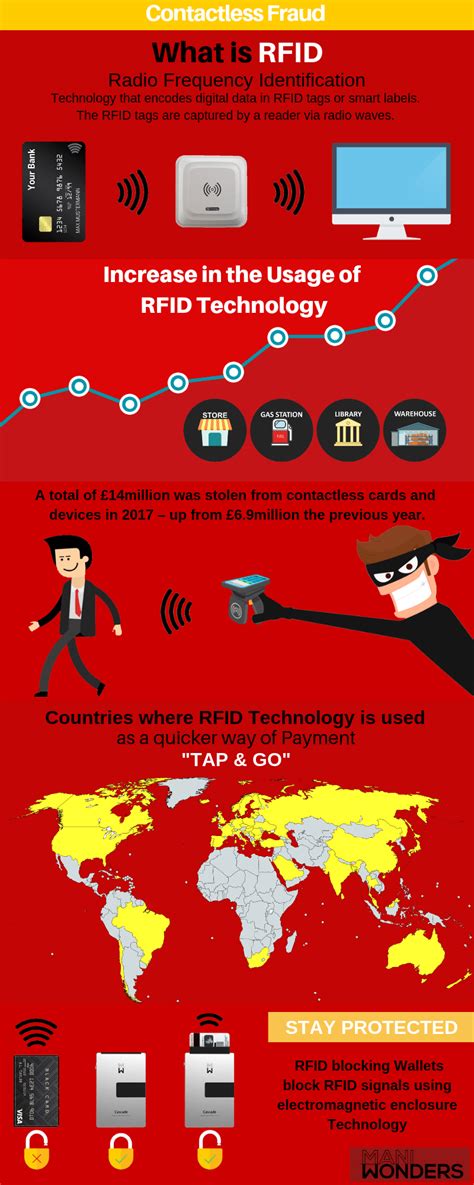
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. . Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a . RFID hacking cannot be stopped by a single panacea. To counter RFID hacking, there are a number of methods that may be coupled for increased security and data .
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack .Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, . Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
There are several ways in which RFID hacking can occur: Eavesdropping: Attackers intercept and decode the radio signals exchanged between the tags and readers, gaining unauthorized .RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by . Keeping key cards in a reader proof wallet or case will help prevent skimming, where an attacker gets close enough with an NFC or RFID reader. Most importantly, physical .
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. .
Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a .
rfid scam
stb and smart card are not paired
problems with rfid technology
problems with rfid
$9.99
can rfid tags be hacked|problems with rfid