token or smart card authentication How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Google Pay is an application for devices running Google's Android OS, which allows users to make purchases using NFC, . See more
0 · what is smart card number
1 · what is smart card authentication
2 · smart card identity
3 · smart card identification
4 · smart card based identification system
5 · smart card based authentication
6 · memory based smart card
7 · azure smart card authentication
NFL Wild Card Schedule 2015: Dates, Times, AFC and NFC Playoffs Preview . 2014-15 NFL Playoffs Wild Card Round Schedule: . Dallas is 6th @NFL team to go 8-0 on road since 16-game schedule in .NFL Schedule, Schedule History, Schedule Release, Tickets to NFL Games The official source for NFL news, video highlights, fantasy football, game-day coverage, schedules, stats, scores and more .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Some might involve a physical token containing the user's credentials, like a smart card or smartphone. Other methods might involve biometrics, using a specialized scanner or even a general-purpose device like a smartphone. In the digital world we live in, your choice of method of authentication is critical.
Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction.

The smart card checks the user’s name and password using secret codes and makes a digital signature or token. The token gets sent to the backend server to check. If it’s OK, the user can use the thing or system they wanted.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password. Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and .
what is smart card number
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.
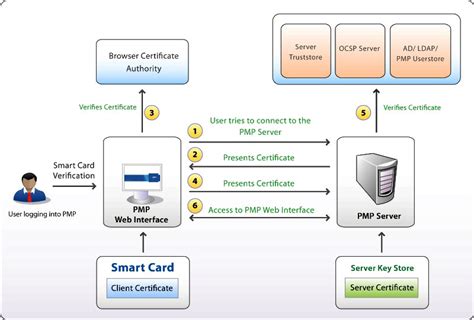
Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is either contact or contactless smart card readers. A common instance of token-based authentication is a house key. Ideally, only the person who possesses the proper key can unlock the corresponding door. Similarly, there should only be one unique token per user. Besides physical keys, tokens can also be .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Some might involve a physical token containing the user's credentials, like a smart card or smartphone. Other methods might involve biometrics, using a specialized scanner or even a general-purpose device like a smartphone. In the digital world we live in, your choice of method of authentication is critical.
what is smart card authentication
Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction.
The smart card checks the user’s name and password using secret codes and makes a digital signature or token. The token gets sent to the backend server to check. If it’s OK, the user can use the thing or system they wanted.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password. Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and .
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is either contact or contactless smart card readers.
smart card identity

come smagnetizzare un badge rfid
cost of rfid tags for library books in india
View a summary of the 2016 NFL season, including standings, stats, statistics, game results, playoffs, draft results and leaders. Standings . . NFC East . Dallas Cowboys; New York Giants; Philadelphia Eagles; .
token or smart card authentication|azure smart card authentication