what do virtual smart cards use for authentication coursehero •Authentication is the process of verifying one’s identity, and it takes place when . Around the Promoted by Taboola. Get the latest 2024 NFL Playoff Picture seeds and scenarios. See the full NFL conference standings and wild card teams as if the season ended today.
0 · Understanding and Evaluating Virtual Smart Cards
1 · Understanding and Evaluating Virtual S
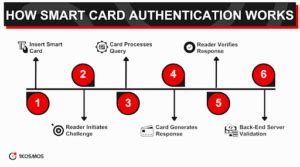
2 · Understanding Smart Card Authentication in Cybersecurity
3 · Understanding Smart Card Authentication
4 · Understanding API Access and Authentication in Web Services
5 · Personal Identity Verification Card 101
6 · Get Started with Virtual Smart Cards
$16.99
Be aware that smart cards: Use public key infrastructure (PKI) technology to store digital signatures, cryptography keys, and identi±cation codes. Can authenticate a user when used in conjunction with a smart card reader connected to a computer system.

making rfid tags obligatory
•Use virtual smart card authentication on a computer named Computer2. •Enable Secure Bo. Virtual smart cards offer comparable security benefits to conventional smart . •Authentication is the process of verifying one’s identity, and it takes place when .

Understanding and Evaluating Virtual Smart Cards
Be aware that smart cards: Use public key infrastructure (PKI) technology to store digital signatures, cryptography keys, and identi±cation codes. Can authenticate a user when used in conjunction with a smart card reader connected to a computer system. Virtual smart cards are a technology from Microsoft that offers comparable security benefits in two-factor authentication to physical smart cards. They also offer more convenience for users and lower cost for organizations to deploy.
Virtual smart cards offer comparable security benefits to conventional smart cards by using two-factor authentication. The technology also offers more convenience for users and has a lower cost to deploy. Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) chip that is available on devices. •Authentication is the process of verifying one’s identity, and it takes place when subjects present suitable credentials to do so. When a user enters the right password with a username, for example, the password verifies that the user is the owner of the username. In a nutshell, authentication establishes the validity of a claimed identity. • In a username-password .•Use virtual smart card authentication on a computer named Computer2. •Enable Secure Boot on a computer named Computer3. •Connect a computer named Computer4 to a projector by using Miracast. •Ensure that a user named User 1 can use keyboard shortcuts by pressing one key at .
Understanding and Evaluating Virtual S
Understanding Smart Card Authentication in Cybersecurity
A virtual smart card improves cybersecurity by adding an extra layer of authentication, ensuring that only authorized users can access sensitive information. It also protects against malware and viruses, as the virtual smart card cannot be physically stolen or damaged.
Study with Quizlet and memorize flashcards containing terms like Which are authentication factors? Choose three answers, What do virtual smart cards use for authentication?, What do physical smart cards use for authentication? and more.
Smart cards provide ways to securely identify and authenticate the holder and third parties who want to gain access to the card. A PIN code or biometric data can be used for authentication. They also provide a way to securely store data on the card and protect communications with encryption. Smart cards provide a portable, easy to use form factor.
Virtual smart cards are created in the TPM, where the keys that are used for authentication are stored in cryptographically secured hardware. By utilizing TPM devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three key properties that are desired for smart cards: non . Be aware that smart cards: Use public key infrastructure (PKI) technology to store digital signatures, cryptography keys, and identi±cation codes. Can authenticate a user when used in conjunction with a smart card reader connected to a computer system. Virtual smart cards are a technology from Microsoft that offers comparable security benefits in two-factor authentication to physical smart cards. They also offer more convenience for users and lower cost for organizations to deploy. Virtual smart cards offer comparable security benefits to conventional smart cards by using two-factor authentication. The technology also offers more convenience for users and has a lower cost to deploy.
Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) chip that is available on devices. •Authentication is the process of verifying one’s identity, and it takes place when subjects present suitable credentials to do so. When a user enters the right password with a username, for example, the password verifies that the user is the owner of the username. In a nutshell, authentication establishes the validity of a claimed identity. • In a username-password .
•Use virtual smart card authentication on a computer named Computer2. •Enable Secure Boot on a computer named Computer3. •Connect a computer named Computer4 to a projector by using Miracast. •Ensure that a user named User 1 can use keyboard shortcuts by pressing one key at .A virtual smart card improves cybersecurity by adding an extra layer of authentication, ensuring that only authorized users can access sensitive information. It also protects against malware and viruses, as the virtual smart card cannot be physically stolen or damaged.
Study with Quizlet and memorize flashcards containing terms like Which are authentication factors? Choose three answers, What do virtual smart cards use for authentication?, What do physical smart cards use for authentication? and more.Smart cards provide ways to securely identify and authenticate the holder and third parties who want to gain access to the card. A PIN code or biometric data can be used for authentication. They also provide a way to securely store data on the card and protect communications with encryption. Smart cards provide a portable, easy to use form factor.
Understanding Smart Card Authentication
Understanding API Access and Authentication in Web Services
Download: NFC Reader and Writer APK (App) - Latest Version: 6.0 - Updated: .Information. NFC Tools GUI is a cross Platform software : it works on Mac, Windows and Linux. You can read and write your NFC chips with a simple and lightweight user interface. Connect your NFC reader to your computer like the very popular ACR122U to start playing with your NFC .
what do virtual smart cards use for authentication coursehero|Understanding and Evaluating Virtual S