rfid chip and sonic attacks Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! Amiibo cards contain NFC chips, which can be scanned using the NFC .
0 · security attacks on rfid
1 · rfid security
2 · rfid hacking tools
3 · rfid blocking wallet
4 · is rfid safe to hack
5 · is rfid hacked
6 · how rfid can you hack
7 · eavesdropping in rfid
Find SEC football radio online broadcasts and streaming audio for all fourteen schools. Find out where Alabama, Arkansas, Auburn, Florida, Georgia, Kentucky, LSU, Mississippi State, Missouri, Ole Miss, South Carolina, Tennessee, Texas .TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of the Tigers, Andy Burcham, weekly guests will include head football coach Hugh Freeze in the fall and head men’s basketball .
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
rfid tag not working
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
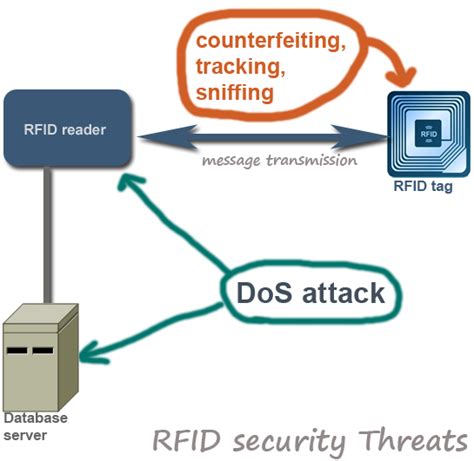
This paper comprehensive analysis the potential security threats and attacks that RFID networks faces, discusses possible countermeasures,reviews the existing RFID system security mechanisms and examines the weaknesses or flaws in these protocols.RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. RFID/NFC-based applications are particularly vulnerable to such attacks. We provide an overview of RFID-based relay attacks and evaluate various streams of research that have attempted to address these attacks.
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.Attacks to the Backend • The memory of a ISO 15693 tag acts like a normal storage • RFDump (Black Hat 2004) could help to manipulate data like with a hex-editor • SQL-Injection and other attacks are possible
The limited power and processing ability of RFID chips makes them vulnerable to attackers operating at a distance. A new protocol could tackle this problem. Due to these security issues, there are several attacks possible on RFID systems such as tag cloning, disclosure, spoofing, and replay attack to name a few. Table 1 shows the various threats on the IoT applications. This paper discusses various attacks on the RFID system. Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful.
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.This paper comprehensive analysis the potential security threats and attacks that RFID networks faces, discusses possible countermeasures,reviews the existing RFID system security mechanisms and examines the weaknesses or flaws in these protocols.
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities.
RFID/NFC-based applications are particularly vulnerable to such attacks. We provide an overview of RFID-based relay attacks and evaluate various streams of research that have attempted to address these attacks. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.Attacks to the Backend • The memory of a ISO 15693 tag acts like a normal storage • RFDump (Black Hat 2004) could help to manipulate data like with a hex-editor • SQL-Injection and other attacks are possible
The limited power and processing ability of RFID chips makes them vulnerable to attackers operating at a distance. A new protocol could tackle this problem.
security attacks on rfid
Accept credit card payments today with the Square Reader for Magstripe. Plug into your phone or tablet and start selling right away. Learn more.
rfid chip and sonic attacks|eavesdropping in rfid